Induced demand is an economic theory that describes how increasing the supply of a product or service can make people want that good even more. When applied to roads, this theory argues that more roads lead to more vehicle traffic. Why? Because new roads will attract new drivers, leading to more traffic on the streets.
This same logic can be applied to mobile traffic and is especially prescient with the dawn of the new 5G network. But while 5G networks hold enormous promise for service provider innovation, they’re simultaneously opening the door for new cybercriminal activity and increased malicious traffic.
As a result, distributed denial of service (DDoS) attacks will continue to grow, both in scale and frequency, and we could soon see a new generation of cybercriminals taking advantage of this more widespread and higher capacity bandwidth.
DDoS Mitigation Skills in Demand
In economic terms, demand refers to how much (quantity) of a product or service is desired by buyers. In the mobile world, defending against DDoS attacks is in high demand— especially as these types of attacks show no signs of going away any time soon.
According Frost & Sullivan’s whitepaper “Service Provider Requirements for DDoS Mitigation,” DDoS attacks are more dangerous, vicious and common than ever – and they are also harder to mitigate. DDoS has become a preferred method for cybercriminals, given how easy they are to launch in the era of the Internet of Things (IoT). Whether motivated by financial gain or political ideology, malicious actors are out to make a profit, a name for themselves, or create chaos. And as the IoT industry grows, DDoS attacks will similarly rise in scale, severity, and frequency. Enterprises, government organizations, and communication service providers (CSPs) should be on the lookout.
In its 2017 technology, media, and telecommunications (TMT) report, Deloitte predicted an average rate of one DDoS attack over 1 Tbps per month. This is a significant increase when you consider that it wasn’t until 2016 when we saw the first-ever dual 1 Tbps attacks. Already in 2018, a US service provider recently suffered the largest DDoS attack ever recorded back in March, peaking at 1.7Tbps. Are 2 Tbps attacks just around the corner?
5G Networks Supplying the Threat
Supply is the amount of goods or services that firms, consumers, laborers, or other economic agents are willing to provide to the marketplace. CSPs are proving to be the suppliers of innovative networks driven by competition and a global race toward 5G.
However, with that innovation comes risk. Parallel to the spread of IoT, the more widespread and higher capacity bandwidth of 5G gives cybercriminals even more opportunity to take advantage. The recent Hikvision authentication security flaw – which gave hackers the ability to potentially hijack cameras, DVRs, and accounts – underscores how the IoT provides hackers with fresh ammunition.
5G will make DDoS an even more attractive attack vector. Wider bandwidth can give more opportunity for hackers looking to spread damage on 5G networks. As a result, CSPs migrating to 5G networks are in a unique position to bake in cybersecurity protections at the network level to help stunt the impact of DDoS attacks.
Reaching Equilibrium with Better Architecture
Economic equilibrium is a state where forces such as supply and demand are balanced, or where the hypothetical supply and demand curves intersect. For telcos, this condition can only be achieved through a holistic approach towards DDoS attacks and 5G networks, rather than relying on outdated defense tactics.
Traditional scrubbing centers, for example, are unable to manage the volume of today’s DDoS traffic. Legitimate traffic is being swept up and blocked, and video streaming quality can be severely impacted. Inline solutions designed primarily for enterprises face the same hurdles, as they don’t scale to the type of traffic loads CSPs experience.
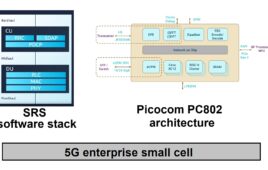
As an alternative, inline high-volume DDoS mitigation combined with deep packet inspection (DPI) is built to meet CSP requirements through reduced costs, visibility and prevention of both inbound and outbound malicious traffic, and faster response time. This solution can be customized, fully virtualized, and fully scaled to keep up with wire speed traffic. Network behavior anomaly detection (NBAD) uses machine learning to detect unknown DDoS attacks and integrated DPI traffic management guarantees assured quality of experience (QoE) during attacks.
Economics Cheat Sheet
Even though 5G benefits both businesses and consumers alike with faster speeds and greater mobility, that additional capacity also presents an opportunity for cybercriminals to exploit.
As we’ve seen with the IoT DDoS attack phenomenon, 5G networks will undoubtedly make these attacks even more destructive. Security will need to be a major focus for telcos, as new innovations make waves – especially 5G.